Malware Is A Serious Threat! Let’s See How To Protect The System From Ransomware!
Ransomware attacks have become normal these days and thus it is needed to protect the system from these attacks. In this article, we will see how we can protect our system from ransomware attacks by just following easy ways.
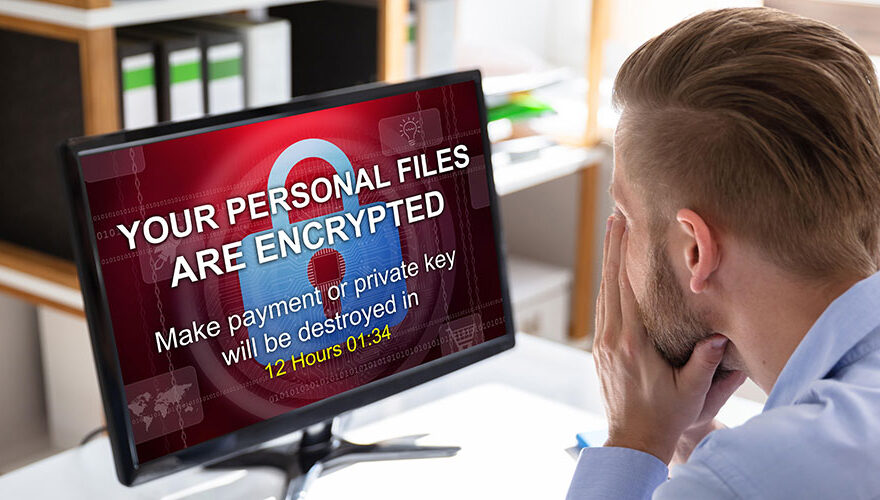
Firstly, we need to understand what ransomware is. Ransomware is a kind of malware that keeps a kind of encryption system which is get employed in the system and holds the user’s information. Anyone sitting in any part of the world can paralyze your entire system if they get succeed in putting malware.
Once a user’s machine is infected by it, ransomware can encrypt all forms of files, ranging even from documents to pictures to videos. And to get the stolen data back from the hackers you have to pay them in millions or sometimes in Bitcoin which is unfair. Thus, it is important to keep your system protected.
Let’s now see some names of dangerous ransomware which are quite popular.
- UIWIX
- WannaCry
- Petya
- Serber
- CryptoWall
We have seen how dangerous malware is. Now, let’s see some ways through which we can protect our system from malware attacks:
Install any legit Antivirus firewall!
This is one of the most common ways to get rid of the malware. With the help of Antivirus, we can choose and create a firewall which is really important. Though, no firewall in the market assures 100% safety from these attacks. But they can be helpful.
So, choose a firewall that fits your budget and assures more safety from Ransomware attacks.
Get Security Awareness Training!
Few people might find it surprising but yes! These kinds of pieces of training are necessary to take if you own a system. There is a reason behind it. Most of the hackers are depend on the human or user simply to gain access. They make users fool easily because most people don’t have basic security knowledge.
By investing in security awareness sessions will help an individual to create a culture of persons who work on the system every day. This will help them to identify and avoid malicious links, dangerous behavior online, and phishing emails.
Read Emails Carefully And Don’t Click On Any Suspicious Link Or Ad!
Be aware of the emails you received. Hackers usually use email ids to send malware to the system. Whenever you get any suspicious mail, just don’t open it delete it. Now, Gmail understands this issue and has started warning about any suspicious activity.
Moreover, if you get any link that seems suspicious to you don’t open it or click on it. Hackers are smart. They just require one click. Avoid suspicious ads you see while browsing.
Choose Specific Application To Whitelist!
You have heard about blacklisting websites or applications which seem damaging your system. Whitelisting is just the opposite of it. It is a practice of giving access to only selected files or software so that no other entity can do any harm.
Just scan your system and select your trusted software to whitelist.
Keep Your Applications Updated!
Whenever you update any application like Adobe, Skype, etc. The updates resolve many security issues and add security patches to the applications. It is tougher to hack a fully updated application than the older one.
Keep those applications updated which keeps your personal information.
Be Prepare After Getting Hacked!
Even if you follow all these ways to protect the system, sometimes hackers get succeed in hacking your system. In this case, you need to prepare a Disaster Recovery Plan (DRS). Follow the below steps:
- Quickly shut down most of the organization’s network immediately to prevent infection from spreading.
- If you are connected with any wifi or Bluetooth just cut them off.
- Inform responsible authorities near you such as cyber police.
- There are two options either pay the ransom to get your files back or don’t pay the ransom and delete all the infected files and restore the new ones using your backup.
So, hope you understood the ways through which you can protect your device from such ransomware attack.